Mamy obecnie Argo CD (czyli wdrażanie stanu z Git). Jenkins wtedy robi typowo CI:
GitLab commit/push (kod w index.php, Dockerfile)
Jenkins:
testy (jeśli są),
build obrazu,
push obrazu do registry (np. OpenShift internal registry),
aktualizacja values-dev.yaml (tag obrazu) w repo Git
Argo CD widzi zmianę w Git i wdraża na healthlog-helm-dev.
Czyli: Jenkins nie wdraża bezpośrednio do klastra (to robi Argo CD). Jenkins tylko „produkuje artefakt” (image) i aktualizuje repo.
Minimalny flow dla Ciebie (najprostszy)
branch: main → produkcja (Argo)
branch: dev lub merge request → dev (Argo)
Jenkins buduje image i podbija tag w kustomize/overlays/dev/values-dev.yaml.
| LP | Nazwa DNS | Adres ip | vCPU | vRAM | vHDD | System Operacyjny | Funkcja |
|---|---|---|---|---|---|---|---|
| 1 | dns1.okdlab.local | 192.168.40.10 | 2 | 2 GB | 16 GB | Fedora Server 43 | DNS dla klastra |
| 2 | proxy.okdlab.local | 192.168.40.15 | 2 | 2 GB | 16 GB | Fedora Server 43 | HAProxy / Load balancer / instalacja |
| 3 | storage.okdlab.local | 192.168.40.20 | 2 | 2 GB | 16/64/128 GB | Fedora Server 43 | Storage NFS dla klastra, registry OpenShift |
| 4 | database-1.okdlab.local | 192.168.40.25 | 2 | 4 GB | 32 GB | Fedora Server 43 | Serwer baz danych PostgreSQL |
| 5 | database-2.okdlab.local | 192.168.40.26 | 2 | 4 GB | 32 GB | Fedora Server 43 | Serwer baz danych MariaDB |
| 6 | bastion.okdlab.local | 192.168.40.30 | 4 | 4 GB | 128 GB | Fedora Server 43 | Instalacja i zarządzanie klastrem OKD |
| 7 | gitlab.okdlab.local | 192.168.40.35 | 4 | 8 GB | 128 GB | Fedora Server 43 | Gitlab |
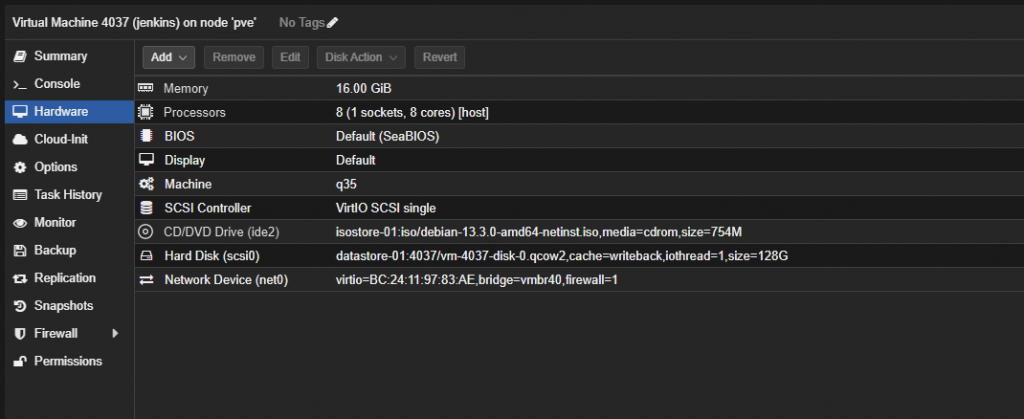
| 8 | jenkins.okdlab.local | 192.168.40.37 | 8 | 16 GB | 256 GB | Fedora Server 43 | Jenkins |
| 9 | bootstrap.testcluster.okdlab.local | 192.168.40.50 | 4 | 16 GB | 128 GB | CentosOS Stream 9 | Bootstrap node |
| 10 | control-plane-1.testcluster.okdlab.local | 192.168.40.51 | 4 | 16 GB | 128 GB | CentosOS Stream 9 | Master node |
| 11 | control-plane-2.testcluster.okdlab.local | 192.168.40.52 | 4 | 16 GB | 128 GB | CentosOS Stream 9 | Master node |
| 12 | control-plane-3.testcluster.okdlab.local | 192.168.40.53 | 4 | 16 GB | 128 GB | CentosOS Stream 9 | Master node |
| 13 | compute-1.testcluster.okdlab.local | 192.168.40.61 | 4 | 16 GB | 256 GB | CentosOS Stream 9 | Worker node |
| 14 | compute-2.testcluster.okdlab.local | 192.168.40.62 | 4 | 16 GB | 256 GB | CentosOS Stream 9 | Worker node |
| 15 | compute-3.testcluster.okdlab.local | 192.168.40.63 | 4 | 16 GB | 256 GB | CentosOS Stream 9 | Worker node |
- https://itadmin.vblog.ovh/klaster-okd-4-19-openshift-serwer-gitlab-pod-argo-cd-i-okd/#Aktualizacja_systemu_i_instalacja_podstawowych_narzedzi
- https://itadmin.vblog.ovh/klaster-okd-4-19-openshift-serwer-gitlab-pod-argo-cd-i-okd/#Ustawienia_swap
- https://itadmin.vblog.ovh/klaster-okd-4-19-openshift-serwer-gitlab-pod-argo-cd-i-okd/#Ustawienia_fastfetch
- https://itadmin.vblog.ovh/klaster-okd-4-19-openshift-serwer-gitlab-pod-argo-cd-i-okd/#Weryfikacja_bledow_przy_starcie_serwera_dmesg
- https://itadmin.vblog.ovh/klaster-okd-4-19-openshift-serwer-gitlab-pod-argo-cd-i-okd/#Tuned_na_Debian_13
- https://itadmin.vblog.ovh/klaster-okd-4-19-openshift-serwer-gitlab-pod-argo-cd-i-okd/#Usuniecie_quiet_%E2%80%9Eladnego_bootowania%E2%80%9D_w_Debian
- https://itadmin.vblog.ovh/klaster-okd-4-19-openshift-serwer-gitlab-pod-argo-cd-i-okd/#Sprawdzenie_ustawien_strefy_czasowej_i_synchronizacji_czasu
- https://itadmin.vblog.ovh/klaster-okd-4-19-openshift-serwer-gitlab-pod-argo-cd-i-okd/#Ustawienia_historii_polecen_uzytkownika_root
Instalacja Jenkins na Debian 13
# aktualizacja i podstawy sudo apt update && sudo apt -y upgrade sudo apt -y install curl ca-certificates gnupg fontconfig # Java 21 (wymagana), Jenkins wymaga Java 21 lub nowszej. sudo apt -y install openjdk-21-jre java -version # dodanie repozytorium Jenkins (LTS) i instalacja sudo mkdir -p /etc/apt/keyrings sudo wget -O /etc/apt/keyrings/jenkins-keyring.asc \ https://pkg.jenkins.io/debian-stable/jenkins.io-2026.key echo "deb [signed-by=/etc/apt/keyrings/jenkins-keyring.asc] \ https://pkg.jenkins.io/debian-stable binary/" | \ sudo tee /etc/apt/sources.list.d/jenkins.list > /dev/null sudo apt update sudo apt -y install jenkins # uruchom i sprawdź status sudo systemctl enable --now jenkins sudo systemctl status jenkins --no-pager # firewall (jeśli masz) sudo ufw allow 8080/tcp sudo ufw reload # pierwszy login (hasło startowe) sudo cat /var/lib/jenkins/secrets/initialAdminPassword http://jenkins.okdlab.local:808
Certyfikat self-signed z SAN
sudo mkdir -p /etc/ssl/okdlab/ca sudo chmod 700 /etc/ssl/okdlab/ca cd /etc/ssl/okdlab/ca # Root CA key sudo openssl genrsa -out okdlab-root-ca.key 4096 sudo chmod 600 okdlab-root-ca.key # Root CA cert (CA:TRUE) sudo openssl req -x509 -new -sha256 -days 3650 \ -key okdlab-root-ca.key \ -out okdlab-root-ca.crt \ -subj "/C=PL/ST=OKDLab/L=OKDLab/O=OKDLab/OU=DevOps/CN=OKDLab Root CA" sudo chmod 644 okdlab-root-ca.crt openssl x509 -in /etc/ssl/okdlab/ca/okdlab-root-ca.crt -noout -text | egrep -i "CA:TRUE|Subject:|Issuer:"
sudo mkdir -p /etc/ssl/okdlab sudo chmod 700 /etc/ssl/okdlab cd /etc/ssl/okdlab # key dla jenkins sudo openssl genrsa -out jenkins.key 4096 sudo chmod 600 jenkins.key
sudo tee jenkins-csr.cnf >/dev/null <<'EOF' [ req ] prompt = no default_md = sha256 distinguished_name = dn req_extensions = v3_req [ dn ] C = PL ST = OKDLab L = OKDLab O = OKDLab OU = DevOps CN = jenkins.okdlab.local [ v3_req ] basicConstraints = CA:FALSE keyUsage = critical, digitalSignature, keyEncipherment extendedKeyUsage = serverAuth subjectAltName = @alt_names [ alt_names ] DNS.1 = jenkins.okdlab.local IP.1 = 192.168.40.37 EOF
# CSR: sudo openssl req -new -key jenkins.key -out jenkins.csr -config jenkins-csr.cnf # Extfile do podpisu (żeby SAN weszło do certu): sudo tee jenkins-cert.ext >/dev/null <<'EOF' basicConstraints = CA:FALSE keyUsage = critical, digitalSignature, keyEncipherment extendedKeyUsage = serverAuth subjectAltName = DNS:jenkins.okdlab.local,IP:192.168.40.37 EOF # Podpis CA: sudo openssl x509 -req -in jenkins.csr \ -CA /etc/ssl/okdlab/ca/okdlab-root-ca.crt \ -CAkey /etc/ssl/okdlab/ca/okdlab-root-ca.key \ -CAcreateserial \ -out jenkins.crt \ -days 825 -sha256 \ -extfile jenkins-cert.ext sudo chmod 644 jenkins.crt # Weryfikacja: openssl verify -CAfile /etc/ssl/okdlab/ca/okdlab-root-ca.crt /etc/ssl/okdlab/jenkins.crt openssl x509 -in /etc/ssl/okdlab/jenkins.crt -noout -issuer -subject
Import certyfikatu na bastion (Fedora 43)
# Na bastionie: scp root@jenkins:/etc/ssl/okdlab/ca/okdlab-root-ca.crt /tmp/okdlab-root-ca.crt sudo cp /tmp/okdlab-root-ca.crt /etc/pki/ca-trust/source/anchors/ sudo update-ca-trust echo | openssl s_client -connect jenkins.okdlab.local:443 -servername jenkins.okdlab.local 2>/dev/null \ | openssl x509 -noout -subject -issuer -fingerprint -sha256 -dates # Sprawdź jaki cert faktycznie serwuje Jenkins (z bastiona) subject=C=PL, ST=OKDLab, L=OKDLab, O=OKDLab, OU=DevOps, CN=jenkins.okdlab.local issuer=C=PL, ST=OKDLab, L=OKDLab, O=OKDLab, OU=DevOps, CN=jenkins.okdlab.local sha256 Fingerprint=6B:AA:7A:B5:08:EE:67:29:F8:E8:5E:2E:10:11:41:20:85:35:71:98:8E:F6:CE:D5:B0:8F:E9:B5:45:02:5A:87 notBefore=Feb 20 17:38:31 2026 GMT notAfter=May 25 17:38:31 2028 GMT # Sprawdź fingerprint certu, który masz w trust store (bastion) openssl x509 -in /etc/pki/ca-trust/source/anchors/jenkins.okdlab.local.crt -noout -fingerprint -sha256
Jenkins za Nginx + HTTPS
sudo systemctl edit jenkins # wklei to co poniżej [Service] Environment="JENKINS_LISTEN_ADDRESS=127.0.0.1" Environment="JENKINS_PORT=8080"
sudo apt -y install nginx nano /etc/nginx/sites-available/jenkins
server {
listen 443 ssl;
server_name jenkins.okdlab.local;
ssl_certificate /etc/ssl/okdlab/jenkins.crt;
ssl_certificate_key /etc/ssl/okdlab/jenkins.key;
location / {
proxy_pass http://127.0.0.1:8080;
proxy_set_header Host $host;
proxy_set_header X-Real-IP $remote_addr;
proxy_set_header X-Forwarded-For $proxy_add_x_forwarded_for;
proxy_set_header X-Forwarded-Proto https;
}
}sudo ln -s /etc/nginx/sites-available/jenkins /etc/nginx/sites-enabled/ sudo nginx -t sudo systemctl restart nginx
Jenkins GUI
Wchodzimy na adres: https://jenkins.okdlab.local/
Hasło pierwszego dostępu: sudo cat /var/lib/jenkins/secrets/initialAdminPassword (na maszynie jenkins.okdlab.local)
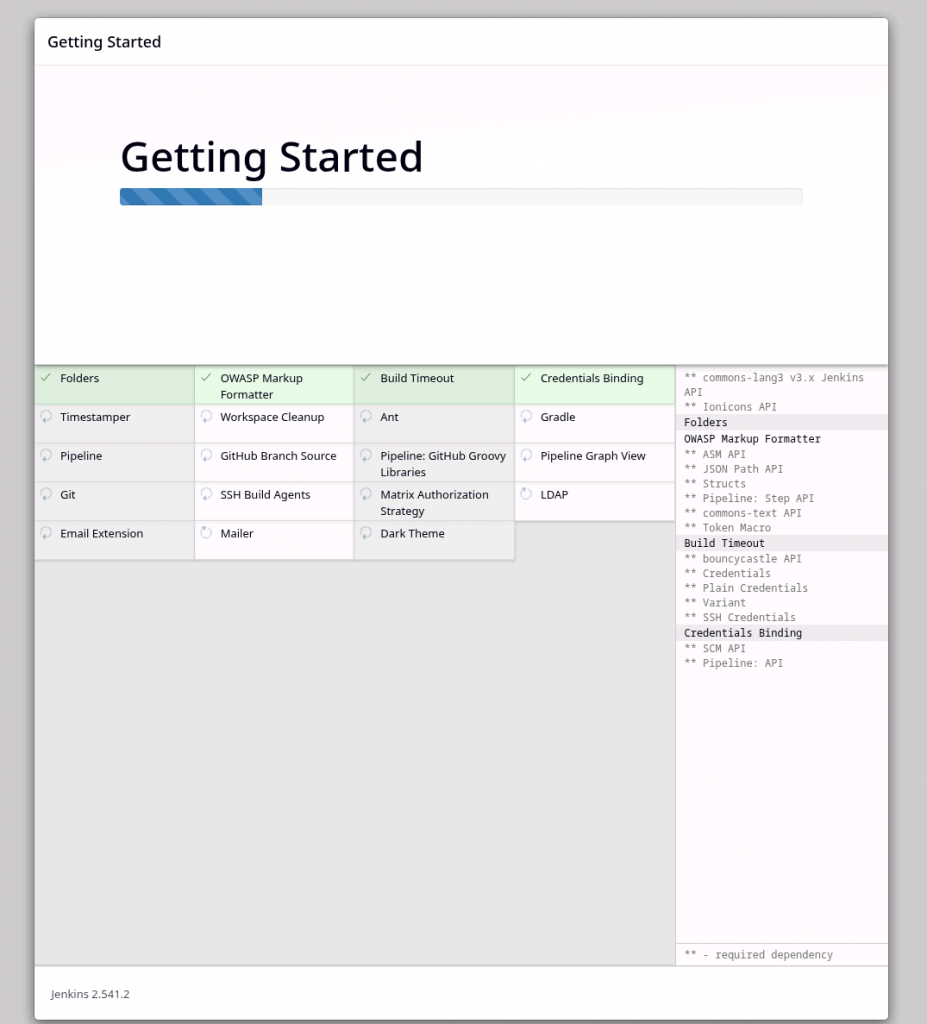
Instalujemy domyślne pluginy.
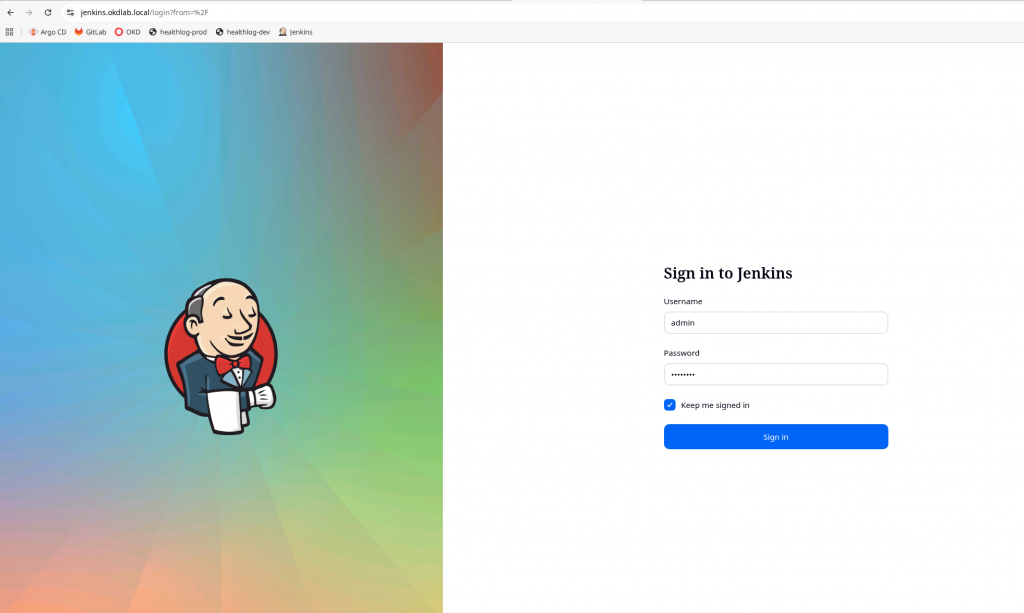
Wchodzimy ponownie na adres: https://jenkins.okdlab.local/
Login: admin (nazwa ustawiona podczas poprzedniego kroku)
Hasło: 1234abcd. (hasło ustawione podczas poprzedniego kroku)